In this assignment we build code to reverse an MD5 hash using a brute force technique where we simply 'forward hash' all possible combinations of characters in strings. This would be similar to a situation where an e-commerce site stored hashed passwords in its database and we somehow have gotten our hands on the database contents and we want to take the hashed password and determine the actual plaintext passwords.
This following is a list of people, and their hashed PIN values.email pin hash_pin ----- --- -------- [email protected] ???? 0bd65e799153554726820ca639514029 [email protected] ???? aa36c88c27650af3b9868b723ae15dfc [email protected] ???? 1ca906c1ad59db8f11643829560bab55 [email protected] ???? 1d8d70dddf147d2d92a634817f01b239 [email protected] ???? acf06cdd9c744f969958e1f085554c8b ...You should be able to easily crack all but one of these these PINs using your application.
The simplest brute force approach generally is done by writing a series of nested loops that go through all possible combinations of characters. This is one of the reasons that password policies specify that you include uppper case, lower case, numbers, and punctuation in passwords is to make brute force cracking more difficult. Significantly increasing the length of the password to something like 20-30 characters is a very good to make brute force cracking more difficult.
You can explore a sample solution for this problem at
http://www.wa4e.com/solutions/crack/
There are several sources of information so you can do the assignment:
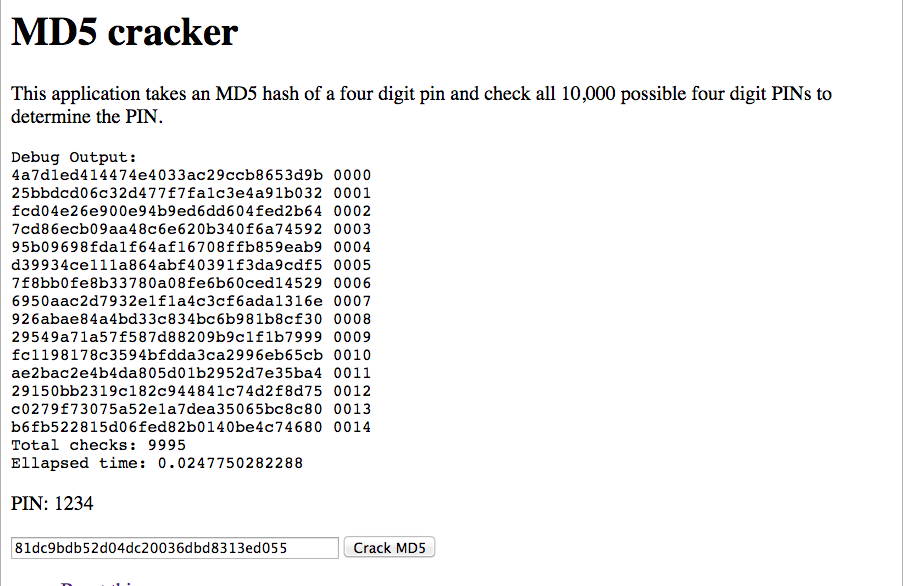
Your application will take an MD5 value like "81dc9bdb52d04dc20036dbd8313ed055" (the MD5 for the string "1234") and check all combinations of four-digit "PIN" numbers to see if any of those PINs produce the given hash.
You will present the user with a form where they can enter an MD5 string and request that you reverse-hash the string. If you can reverse hash the string, print out the PIN:
PIN: 1234
If the string
does not reverse hash to a four digit number simply put out a message like:
PIN: Not found
You must check all four-digit combinations. You must hash the value as a string not as an integer. For example, this shows the right and wrong way to check the hash for "1234":
$check = hash('md5', '1234'); // Correct - hashing a string
$check = hash('md5', 1234); // Incorrect - hashing an integer
You should also print out the first 15 attempts to reverse-hash including both the MD5 value and PIN that you were testing. You should also print out the elapsed time for your computation as shown in the sample application.
In order to make the assignments more consistent, please follow these technical guidelines:
<input type="text" name="md5" size="40">
For this assignment you will hand in:
Please review carefully. The actual points are less important and useful comments about what might be wrong and need fixing. You cannot re-submit your assignment unless the instructor allows you to resubmit.
The total number of points for this assignment is 10. You will get up to 5 points from your instructor. You will get up to 3 points from your peers. You will get 1 for each peer assignment you assess. You need to grade a minimum of 2 peer assignments. You can grade up to 5 peer assignments if you like.
This section is entirely optional and is here in case you want to explore a bit more deeply and test your code skillz.
Here are some possible improvements:
At some point you might run into a time out where PHP decides that your code is running too long and blows up your application. You can check the variable max_execution_time in your PHPInfo screen to see how many seconds PHP will let your code run before aborting it.
Provided by:
www.wa4e.com